What is dust?
In the language of cryptocurrencies, the term dust refers to a tiny amount of coins or tokens – an amount that is so small that most users don’t even notice. Taking Bitcoin as an example, the smallest unit of BTC is 1 satoshi (0.00000001 BTC), so we may use the term dust to refer to a couple of hundreds of satoshis.
What is a dusting attack?
A dusting attack is an attack in which a trace amount of crypto, called dust, is sent to thousands — sometimes even hundreds of thousands — of wallet addresses. This attack is deployed in order to track these addresses with the hope of “un-masking” or de-anonymizing them. Dust is found on most public blockchains, including Bitcoin, Litecoin, Bitcoin Cash, and Dogecoin, among others.
Dusting can be used for various purposes, including:
- Mass Messaging: Blockchain transactions can carry data with them, making it possible to embed messages in dust transactions. This makes dusting usable as an equivalent to an email blast.
- Stress Testing: A dust transaction is a cheap transaction on the blockchain. Dusting can be used to stress test the throughput and capacity of a blockchain network.
- Spamming: Like stress testing, spamming takes advantage of the low cost of dust transactions. Stress testing and spamming are often indistinguishable because they perform the same action for different purposes (i.e. research vs. Denial of Service).
- Wallet Deanonymization: Dust can’t be spent without combining it with a user’s other funds. For this reason, it can be tracked to deanonymize blockchain accounts.
Dusting is not always malicious. However, one of the more common uses for dusting is breaking the anonymity of blockchain accounts.
Dusting for Deanonymization
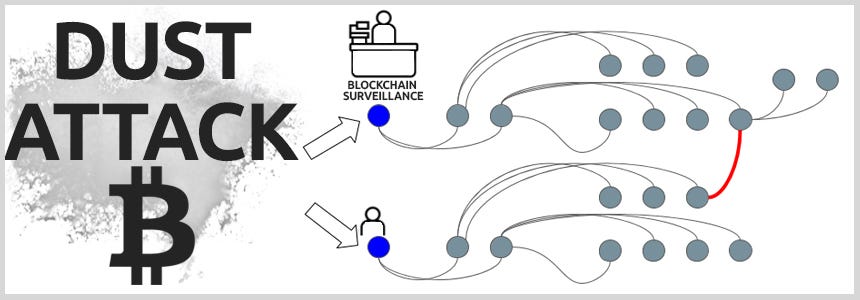
Dusting attacks were developed as a way of breaking the anonymity of the blockchain. In theory, it should be infeasible to determine if two blockchain wallets are owned by the same user. In practice, analysis of transactions and patterns of life on the blockchain can break anonymity.
Dusting helps with this because dust cannot be used independently for a transaction because its value is less than the transaction fee.
For this reason, a user needs to combine dust with other holdings to use it within a transaction. If a blockchain transaction combines dust from one address with a user’s holdings in another, then someone analyzing the transaction history on the blockchain knows that both addresses are owned by the same person.
Who Would Perform a Dusting Attack?
There are a number of groups that perform dusting attacks. Criminals have used dusting attacks to de-anonymize those with large cryptocurrency holdings. Those with large holdings can be targeted in a number of ways, including through phishing scams and cyber extortion. Users with large crypto holdings in high-risk areas could also be physically targeted, or even have a family member kidnapped for a cryptocurrency ransom.
A branch of the government such as a tax or law enforcement agency may also perform a dusting attack in order to connect a person or group to an address. Specifically, they may target gangs that deal in contraband, large criminal networks, money launderers, or tax evaders. Mass dusting is also used by blockchain analytics firms, who study crypto dust for academic purposes or have contracts with government agencies.
Importantly, the person or group that executes the dusting attack and the party that analyzes the results don’t need to be the same. Because it’s on the blockchain, anyone with the skills, tools, and time can analyze the crypto dust after an attack. A criminal organization could study a government’s dusting, or a blockchain analytics firm could study a malicious actor’s dusting.
For this reason, not all dust attacks are considered “attacks.” The mass spreading of dust has also been used to advertise to cryptocurrency users, primarily by sending out messages included in the crypto dust, comparable to an email blast. You may know that the genesis block of Bitcoin (the first block of bitcoin ever mined) included a message.
These mass dustings may also be used as stress tests, where a large amount of crypto dust is sent in a short amount of time to test the throughput, or bandwidth, of a network. Dustings are also sometimes used as a way to spam a network, by sending huge batches of worthless transactions that clog and slow it down considerably. Whatever the intended purpose, mass dustings can be analyzed for various purposes, both good or bad.
Dusting can also be used as a defensive tool. Let’s say that a large criminal enterprise receives a tip that the authorities are closing in on them. The cyber criminals could dust numerous random wallets to spread the dirty money around in an attempt to throw the authorities off their trail.
There is some debate about how traceable addresses are in dusting attacks. As blockchain analytics improve, better countermeasures emerge. Many governments and firms consider their technology as proprietary and keep it closely guarded. Can you still be traced through dusting despite the various precautions available? We really don’t know yet.
Protecting against Dusting Attacks and How to avoid it?
The simplest defense against dusting attacks is to not use dust sent to a blockchain account.
Many wallets have been updated to protect against dusting attacks by identifying funds from transactions below a given threshold as dust and marking them as “Do Not Spend”. While this means that a user can’t use all of the funds at an address, the value of the dust is negligible.
Users can also protect their anonymity on the blockchain by Using a hierarchical-deterministic (HD) wallet, which creates new addresses each time you transact, making it harder to trace you. Some wallets also show dust UTXOs (unspent transaction outputs), which you can mark “do not spend.” These small amounts are then left in your wallet, and if you never use them, no one can track where they go. Others wallets only go online using the Tor Network or a VPN.

